Table of Contents

Getty Images
On Tuesday, Microsoft in-depth an ongoing massive-scale phishing marketing campaign that can hijack person accounts when they’re guarded with multi-issue authentication measures developed to protect against such takeovers. The threat actors guiding the operation, who have focused 10,000 companies because September, have utilized their covert accessibility to sufferer e-mail accounts to trick workers into sending the hackers cash.
Multi-element authentication—also known as two-component authentication, MFA, or 2FA—is the gold typical for account security. It necessitates the account consumer to prove their identity in the form of a thing they have or management (a actual physical protection critical, a fingerprint, or encounter or retina scan) in addition to something they know (their password). As the rising use of MFA has stymied account-takeover strategies, attackers have uncovered methods to strike back.
The adversary in the center
Microsoft noticed a campaign that inserted an attacker-controlled proxy internet site amongst the account users and the perform server they tried to log into. When the person entered a password into the proxy web page, the proxy web site despatched it to the actual server and then relayed the actual server’s response back to the consumer. When the authentication was concluded, the threat actor stole the session cookie the legit web page sent, so the person isn’t going to want to be reauthenticated at every new webpage frequented. The marketing campaign started with a phishing electronic mail with an HTML attachment foremost to the proxy server.
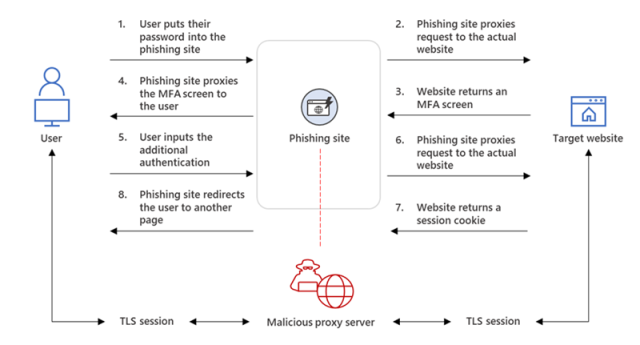
“From our observation, just after a compromised account signed into the phishing website for the to start with time, the attacker utilised the stolen session cookie to authenticate to Outlook on the web (outlook.business.com),” customers of the Microsoft 365 Defender Investigate Group and the Microsoft Menace Intelligence Centre wrote in a blog article. “In various cases, the cookies had an MFA declare, which means that even if the organization had an MFA plan, the attacker made use of the session cookie to achieve accessibility on behalf of the compromised account.”
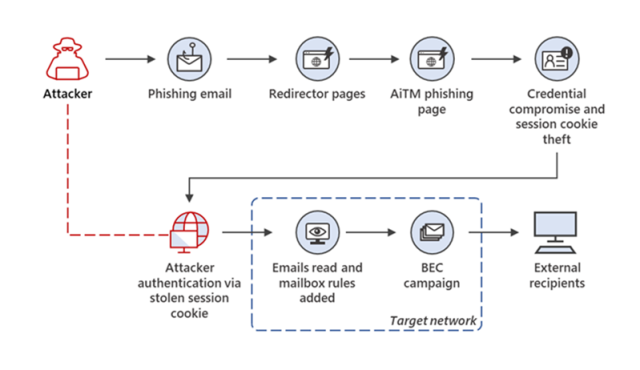
In the times following the cookie theft, the risk actors accessed personnel electronic mail accounts and looked for messages to use in business enterprise e-mail compromise scams, which tricked targets into wiring huge sums of dollars to accounts they thought belonged to co-workers or enterprise partners. The attackers made use of those people email threads and the hacked employee’s forged identity to convince the other bash to make a payment.
To maintain the hacked employee from discovering the compromise, the risk actors created inbox rules that instantly moved certain e-mail to an archive folder and marked them as examine. Above the future couple times, the danger actor logged in periodically to look at for new e-mail.
“On just one celebration, the attacker carried out numerous fraud tries at the same time from the similar compromised mailbox,” the weblog authors wrote. “Every single time the attacker uncovered a new fraud concentrate on, they up-to-date the Inbox rule they developed to involve these new targets’ business domains.”
Microsoft
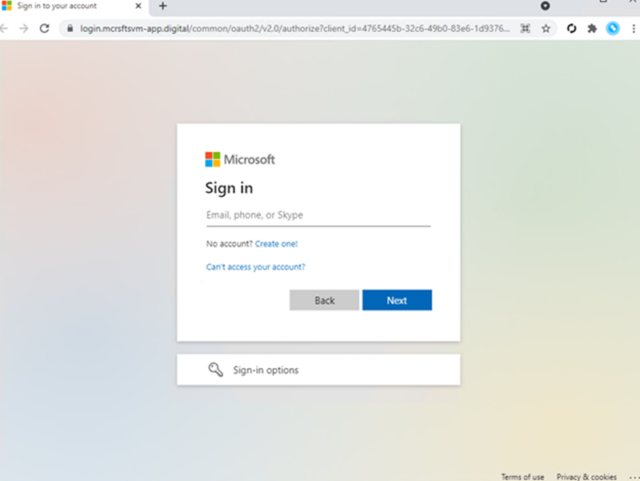
It’s so easy to drop for ripoffs
The website put up exhibits how easy it can be for employees to tumble for these ripoffs. The sheer volume of e-mail and workload usually can make it tricky to know when a concept is authentic. The use of MFA currently indicators that the person or group is training good security cleanliness. Just one of the number of visually suspicious components in the fraud is the area name made use of in the proxy internet site landing web site. Still, given the opaqueness of most corporation-particular login webpages, even the sketchy area title could possibly not be a useless giveaway.
Microsoft
Almost nothing in Microsoft’s account should be taken to say that deploying MFA just isn’t a person of the most powerful actions to prevent account takeovers. That claimed, not all MFA is equivalent. A person-time authentication codes, even when despatched by SMS, are far better than very little, but they continue to be phishable or interceptable by means of much more exotic abuses of the SS7 protocol applied to send textual content messages.
The most powerful sorts of MFA readily available are individuals that are compliant with criteria set by the marketplace-huge FIDO Alliance. These varieties of MFA use a bodily protection key that can appear as a dongle from businesses like Yubico or Feitian or even an Android or iOS machine. The authentication can also appear from a fingerprint or retina scan, neither of which at any time depart the finish-user gadget to avoid the biometrics from remaining stolen. What all FIDO-appropriate MFA has in common is that it can not be phished and takes advantage of back-finish techniques resistant to this sort of ongoing marketing campaign.




More Stories
Will Crypto-Based E-Commerce Destroy the Dinosaur-Style Banking Industry?
Getting Started With Crypto
Everything You Need to Know About Davenport Laroche